If an external auditor arrived tomorrow, could you, as the CIO, explain your ColdFusion security posture clearly, with evidence and without scrambling?
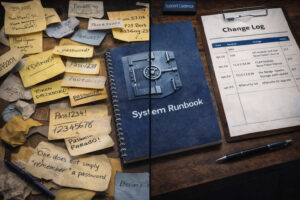
Which of the two illustrates your cf security logs? Which do you think would survive an audit?
Boards and CEOs want documented controls. Cyber insurers raise the bar during underwriting. Regulators look for proof, not context. A single high-risk finding can turn into an awkward conversation with the CEO, fast.
ColdFusion can run securely. It’s governance that makes all the difference.
Where audit exposure shows up
Many ColdFusion environments develop the same pressure points over time:
- ColdFusion and Java versions drift behind
- Hotfixes land reactively, without a repeatable schedule
- Authentication and session settings accumulate through years of change
- Security decisions live in people’s heads, not in documentation, creating key-person risk
- Disaster recovery exists as a plan, not as a practiced procedure
Auditors treat an untested restore as a missing control. Security and uptime get evaluated together. Mess those two up, and everything looks like a guessing game.
Security teams raise findings. The board asks for a plan. The company ends up debating the platform instead of presenting risk controls and a roadmap.
That dynamic creates leadership risk. It’s all totally avoidable.
What audit-defensible looks like
Audit-defensible postures in CF require clarity and repeatability. That usually includes:
- A complete inventory of ColdFusion versions in use, with ownership and purpose
- A documented patch cadence, plus evidence and sign-off from the last two cycles
- Intentional access control, including privileged paths and administrative tools
- A tested disaster recovery process with written results, including Recovery Time Objective (RTO) and Recovery Point Objective (RPO)
Explainable, logically consistent architecture signals security maturity. When the story seems muddled, auditors assume higher risk.
A quick self-check for ColdFusion CIOs
If you want a fast signal before bringing in outside help, start here:
- Can you list every ColdFusion instance and version, and confirm it in an inventory?
- Can you show the last two patch cycles with evidence and approvals?
- Can you provide a list of administrative access and the corresponding review dates?
- Can you prove a restore works, with written results and timed outcomes?
Any fuzzy answer represents an audit exposure point.
The outcome CIOs want
A win for the CIO looks like operational control and executive confidence:
- Predictable costs and planning
- Fewer urgent fixes and fire drills
- A board-ready narrative with metrics (mean time to patch, restore test success rate with Recovery Time Objective (RTO) and Recovery Point Objective (RPO), and privileged access review cadence)
- Vendor leverage through options and preparation
The goal is a posture you can defend with confidence in one meeting, backed by proof.
Not sure what to do next?
If you want an outside perspective on whether your ColdFusion app is audit-defensible, schedule a 15-minute conversation with me, the CEO of TeraTech
You’ll get a clear snapshot of audit exposure points, a short risk register, and a practical 30/60/90-day plan you can share with leadership.